February/2023 Latest Braindump2go 400-007 Exam Dumps with PDF and VCE Free Updated Today! Following are some new Braindump2go 400-007 Real Exam Questions!
QUESTION 83
Which statement about hot-potato routing architecture design is true?
A. Hot-potato routing is the preferred architecture when connecting to content providers
B. Hop-potato keeps traffic under the control of the network administrator for longer
C. OSPF uses hot-potato routing if all ASBRs use the same value for the external metric
D. Hot-potato routing is prone to misconfiguration as well as poor coordination between two networks
Answer: A
QUESTION 84
Two enterprise networks must be connected together. Both networks are using the same private IP addresses.
The client requests from both sides should be translated using hide NAT (dynamic NAT) with the overload feature to save IF addresses from the NAT pools.
Which design addresses this requirement using only one Cisco I OS NAT router for both directions?
A. This is not possible, because two Cisco IOS NAT routers are required to do dynamic NAT, with overload in both directions.
B. The ip nat inside and ip nat outside commands must be configured at the interfaces with the overload option in both directions.
C. The overload feature is the default and does not have to be configured.
D. Two different NAT pools must be used for the ip nat inside source and the ip nat outside source commands for the overload feature in both directions.
E. The Nat Virtual interface must be used to achieve this requirement.
Answer: D
QUESTION 85
Refer to the exhibit. As part of a redesign project, you must predict multicast behavior.
What happens to the multicast traffic received on the shared tree (*,G), if it is received on the LHR interface indicated*?

A. It is dropped due to an unsuccessful RPF check against the multicast source
B. It is switched give that no RPF check is performed
C. It is switched due to a successful RPF check against the routing table
D. It is dropped due to an unsuccessful RPk8t8ck against the multicast receiver.
Answer: A
QUESTION 86
A BGP route reflector in the network is taking longer than expected to coverage during large network changes.
Troubleshooting shows that the router cannot handle all the TCP acknowledgements during route updates.
Which action can be performed to tune the device performance?
A. Increase the size of the hold queue.
B. Increase the size of the large buffers.
C. Decrease the size of the small buffers.
D. Increase the keepalive timers for each BGP neighbor.
Answer: A
QUESTION 87
Which two application requirements are mandatory tor traffic to receive proper treatment when placed in the priority queue? (Choose two.)
A. small transactions (HTTP-like behavior)
B. WRED drop treatment
C. tolerance to packet loss
D. intolerance to jitter
E. TCP-based application
Answer: CD
QUESTION 88
Which two conditions must be met for EIGRP to maintain an alternate loop-free path to a remote network? (Choose two.)
A. The Reported Distance from a successor is lower than the local Feasible Distance.
B. The Reported Distance from a successor is higher than the local Feasible Distance.
C. The feasibility condition does not need to be met.
D. The Feasible Distance from a successor is lower than the local Reported Distance.
E. A feasible successor must be present.
Answer: AE
QUESTION 89
You are designing a new Ethernet-based metro-area network for an enterprise customer to connect 50 sites within the same city OSPF will be the routing protocol used. The customer is primarily concerned with IPv4 address conservation and convergence time.
Which two combined actions do you recommend? (Choose two)
A. Use a multipoint Metro-E service for router connections
B. Use a single address per router for all P2P links
C. Use P2P links between routers in a hub-and-spoke design
D. Configure address aggregation at each site router
E. Determine which OSPF routers will be DR/BDR
Answer: AC
QUESTION 90
Which two statements about MLD snooping are true? (Choose two)
A. When MLD snooping is enabled, QoS is automatically enabled.
B. A VLAN can support multiple active MLD snooping queries, as long as each one is associated to a different multicast group.
C. AN MLD snooping querier election occurs when any MLD snooping querier goes down or if there is an IP address change on the active querier.
D. When multiple MLD snooping queriers are enabled in a VLAN, the querier with the lowest IP address in the VLAN is elected as the active MLD snooping querier.
Answer: CD
QUESTION 91
Which two design option are available to dynamically discover the RP in an IPv6 multicast network? (Choose two)
A. embedded RP
B. MSDP
C. BSR
D. Auto-RP
E. MLD
Answer: AC
QUESTION 92
Company A has a hub-and spoke topology over an SP-managed infrastructure. To measure traffic performance metrics. IP SLA senders on all spoke CE routers and an IP SLA responder on the hub CE router.
What must they monitor to have visibility on the potential performance impact due to the constantly increasing number of spoke sites?
A. memory usage on the hub router
B. interface buffers on the hub and spoke routers
C. CPU and memory usage on the spoke routers
D. CPU usage on the hub router
Answer: D
QUESTION 93
Which two descriptions of CWDM are true? (Choose two)
A. typically used over long distances, but requires optical amplification
B. uses the 850nm band
C. allows up to 32 optical earners to be multiplexed onto a single fiber
D. shares the same transmission window as DWDM
E. Passive CWDM devices require no electrical power
Answer: DE
QUESTION 94
SDWAN networks capitalize the usage of broadband Internet links over traditional MPLS links to offer more cost benefits to enterprise customers. However, due to the insecure nature of the public Internet, it is mandatory to use encryption of traffic between any two SDWAN edge devices installed behind NAT gateways.
Which overlay method can provide optimal transport over unreliable underlay networks that are behind NAT gateways?
A. TLS
B. DTLS
C. IPsec
D. GRE
Answer: C
QUESTION 95
Company XYZ runs OSPF in their network. A design engineer decides to implement hot-potato routing architecture.
How can this implementation be achieved?
A. Enable iBGP and apply prepend to ensure all prefixes will have the same length of the AS path attribute value.
B. Redistribute the external prefixes onto OSPF and ensure the total metric calculation includes only the ext value and the value is the same in all ASBRs.
C. Enable OSPF load-balancing over unequal cost path.
D. Redistribute the external prefixes onto OSPF and ensure that the total metric calculation includes external internal values.
Answer: D
QUESTION 96
What are two primary design constraints when a robust infrastructure solution is created? (Choose two.)
A. monitoring capabilities
B. project time frame
C. staff experience
D. component availability
E. total cost
Answer: BE
QUESTION 97
SD-WAN can be used to provide secure connectivity to remote offices, branch offices, campus networks, data centers, and the cloud over any type of IP-based underlay transport network. Which two statements describe SD WAN solutions? (Choose two.)
A. SD-WAN networks are inherently protected against slow performance.
B. Control and data forwarding planes are kept separate.
C. Improved operational efficiencies result In cost savings.
D. Solutions include centralized orchestration, control, and zero-touch provisioning.
E. Solutions allow for variations of commodity and specialized switching hardware.
Answer: CD
QUESTION 98
An architect designs a multi-controller network architecture with these requirements:
– Achieve fast failover to control traffic when controllers fail.
– Yield a short distance and high resiliency in the connection between the switches and the controller.
– Reduce connectivity loss and enable smart recovery to improve the SDN survivability.
– Improve connectivity by adding path diversity and capacity awareness for controllers.
Which control plane component of the multi-controller must be built to meet the requirements?
A. control node reliability
B. controller stale consistency
C. control path reliability
D. controller clustering
Answer: D
QUESTION 99
Company XYZ is planning to deploy primary and secondary (disaster recovery) data center sites. Each of these sites will have redundant SAN fabrics and data protection is expected between the data center sites. The sites are 100 miles (160 km) apart and target RPO/RTO are 3 hrs and 24 hrs, respectively. Which two considerations must Company XYZ bear in mind when deploying replication in their scenario? (Choose two.)
A. Target RPO/RTO requirements cannot be met due to the one-way delay introduced by the distance between sites.
B. VSANs must be routed between sites to isolate fault domains and increase overall availability.
C. Synchronous data replication must be used to meet the business requirements.
D. Asynchronous data replication should be used in this scenario to avoid performance impact in the primary site.
E. VSANs must be extended from the primary to the secondary site to improve performance and availability.
Answer: CD
Explanation:
RPO and RTO tend to vary based on the application involved. These metrics tend to fluctuate between data that cannot be lost (i.e., low RPO but high RTO) such as financial and healthcare data as well as real-time systems that cannot be down (i.e., high RPO but low RTO) such as an E-commerce web server.
QUESTION 100
Which undesired effect of increasing the jitter compensation buffer is true?
A. The overall transport jitter decreases and quality improves.
B. The overall transport jitter increases and quality issues can occur.
C. The overall transport delay increases and quality issues can occur.
D. The overall transport delay decreases and quality improves.
Answer: C
QUESTION 101
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
A. flow-based analysis to measure bandwidth mix of applications and their flows
B. call management analysis to identify network convergence-related failures
C. call management analysis to identify CAC failures and call quality issues
D. active monitoring via synthetic probes to measure loss, latency, and jitter
E. passive monitoring via synthetic probes to measure loss, latency, and jitter
F. flow-based analysis with PTP time-stamping to measure loss, latency, and jitter
Answer: ACD
QUESTION 102
Which two advantages of using DWDM over traditional optical networks are true? (Choose two.)
A. inherent topology flexibility and service protection provided without penalty through intelligent oversubscription of bandwidth reservation
B. ability to expand bandwidth over existing optical Infrastructure
C. inherent topology flexibility with built-in service protection
D. inherent topology flexibility with intelligent chromatic dispersion
E. inherent topology flexibility with a service protection provided through a direct integration with an upper layer protocol
Answer: AB
QUESTION 103
Refer to the exhibit. This network is running OSPF and EIGRP as the routing protocols. Mutual redistribution of the routing protocols has been configured on the appropriate ASBRs. The OSPF network must be designed so that flapping routes in EIGRP domains do not affect the SPF runs within OSPF. The design solution must not affect the way EIGRP routes are propagated into the EIGRP domains. Which technique accomplishes the requirement?
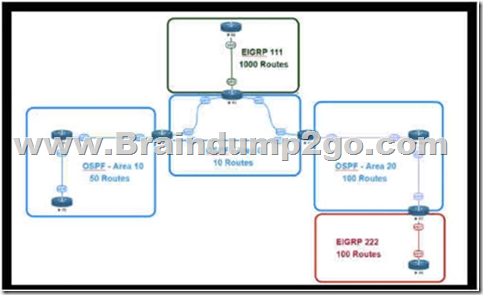
A. route summarization the ASBR interfaces facing the OSPF domain
B. route summarization on the appropriate ASBRS.
C. route summarization on the appropriate ABRS.
D. route summarization on EIDRP routers connecting toward the ASBR
Answer: D
QUESTION 104
Company XYZ is running OSPF in their network. They have merged with another company that is running EIGRP as the routing protocol. Company XYZ now needs the two domains to talk to each other with redundancy, while maintaining a loop free environment.
The solution must scale when new networks are added into the network in the near future.
Which technology can be used to meet these requirements?
A. multipoint route-redistribution with route filtering using ACLs
B. multipoint route-redistribution with route filtering using route tags
C. single point route-redistribution with route filtering using route tags
D. single point route-redistribution with route filtering using ACLs
Answer: B
QUESTION 105
Company XYZ is in the process of identifying which transport mechanism(s) to use as their WAN technology.
Their main two requirements are.
– a technology that could offer DPI, SLA, secure tunnels, privacy, QoS, scalability, reliability, and ease of management
– a technology that is cost-effective
Which WAN technology(ies) should be included in the design of company XYZ?
A. Software-defined WAN should be the preferred choice because it complements both technologies, covers all the required features, and it is the most cost-effective solution.
B. Internet should be the preferred option because it is cost effective and supports BFD, IP SLA. and IPsec for secure transport over the public Internet.
C. Both technologies should be used. Each should be used to back up the other one; where the primary links are MPLS, the internet should be used as a backup link with IPsec (and vice versa).
D. MPLS meets all these requirements and it is more reliable than using the Internet. It is widely used with defined best practices and an industry standard.
Answer: A
QUESTION 106
Which MPLS TE design consideration is true?
A. MPLS TE replaces LDP and the dependency of the IGP to identify the best path.
B. MPLS TE provides link and node protection
C. MPLS TE optimizes the routing of IP traffic, given the constraints imposed by backbone capacity and application requirements.
D. MPLS TE requires Layer 3 VPN full-mesh topology deployment
Answer: C
QUESTION 107
The network designer needs to use GLOP IP address in order make them unique within their ASN, which multicast address range will be considered?
A. 239.0.0.0 to 239.255.255.255
B. 224.0.0.0 to 224.0.0.255
C. 233.0.0.0 to 233.255.255.255
D. 232.0.0.0 to 232.255.255.255
Answer: C
QUESTION 108
Drag and Drop Question
Drag and drop the multicast protocols from the left onto the current design situation on the right.
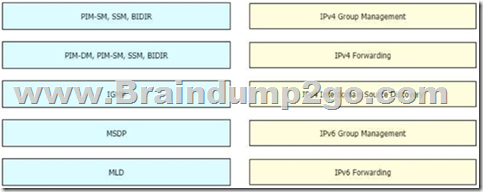
Answer:

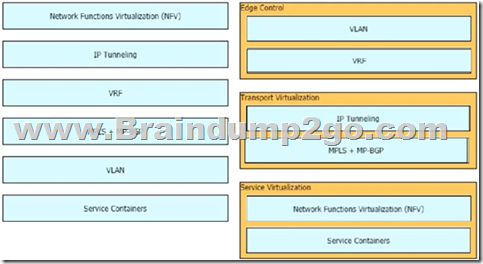
QUESTION 109
Drag and Drop Question
Drag and drop the end-to-end network virtualization elements from the left onto the correct network areas on the right.
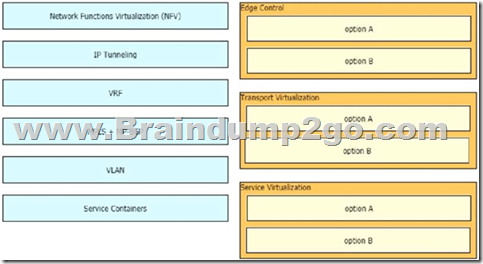
Answer:
QUESTION 110
Which two data plane hardening techniques are true? (Choose two)
A. warning banners
B. redundant AAA servers
C. Control Plane Policing
D. SNMPv3
E. infrastructure ACLs
F. disable unused services
G. routing protocol authentication
Answer: CE
QUESTION 111
You have been asked to design a high-density wireless network for a university campus.
Which two principles would you apply in order to maximize the wireless network capacity? (Choose two.)
A. Implement a four-channel design on 2.4 GHz to increase the number of available channels
B. Choose a high minimum data rate to reduce the duty cycle.
C. increases the number of SSlDs to load-balance the client traffic.
D. Make use of the 5-GHz band to reduce the spectrum utilization on 2.4 GHz when dual-band clients are used.
E. Enable 802.11n channel bonding on both 2.4 GHz and 5 GHz to increase the maximum aggregated cell throughput.
Answer: BD
QUESTION 112
Company XYZ is redesigning their QoS policy. Some of the applications used by the company are real- time applications. The QoS design must give these applications preference in terms of transmission. Which QoS strategy can be used to fulfill the requirement?
A. weighted fair queuing
B. weighted random early detection
C. low-latency queuing
D. first-in first-out
Answer: C
QUESTION 113
As part of workspace digitization, a large enterprise has migrated all their users to Desktop as a Sen/ice (DaaS), by hosting the backend system in their on-premises data center. Some of the branches have started to experience disconnections to the DaaS at periodic intervals, however, local users in the data center and head office do not experience this behavior.
Which technology can be used to mitigate this issue?
A. tail drop
B. traffic shaping
C. WRED
D. traffic policing
Answer: B
QUESTION 114
A healthcare provider discovers that protected health information of patients was altered without patient consent. The healthcare provider is subject to HIPAA compliance and is required to protect PHI data.
Which type of security safeguard should be implemented to resolve this issue?
A. technical and physical access control
B. administrative security management processes
C. physical device and media control
D. technical integrity and transmission security
Answer: D
QUESTION 115
Which two technologies enable multilayer segmentation? (Choose two.)
A. policy-based routing
B. segment routing
C. data plane markings
D. firewalls
E. filter lists
Answer: AD
QUESTION 116
IPFIX data collection via standalone IPFIX probes is an alternative to flow collection from routers and switches.
Which use case is suitable for using IPFIX probes?
A. performance monitoring
B. security
C. observation of critical links
D. capacity planning
Answer: A
QUESTION 117
Company XYZ wants to use the FCAPS ISO standard for network management design.
The focus of the design should be to monitor and keep track of any performance issues by continuously collecting and analyzing statistical information to monitor, correct, and optimize any reduced responsiveness across the network.
Which layer accomplishes this design requirement?
A. fault management
B. accounting management
C. performance management
D. security management
Answer: C
QUESTION 118
While designing a switched topology, in which two options is UplinkFast recommended? (Choose two )
A. when switches of different spanning-tree types are connected (for example. 802.1d connecting to 802.1w)
B. on distribution layer switches
C. when hello timers are changed to more aggressive values
D. on access layer switches
E. on the core switches
Answer: AD
QUESTION 119
You are using iSCSI to transfer files between a 10 Gigabit Ethernet storage system and a 1 Gigabit Ethernet server.
The performance is only approximately 700 Mbps and output drops are occurring on the server switch port.
Which action will improve performance in a cost-effective manner?
A. Change the protocol to CIFS.
B. Increase the queue to at least 1 GB
C. Use a WRED random drop policy
D. Enable the TCP Nagle algorithm on the receiver
Answer: A
QUESTION 120
Customer XYZ network consists of an MPLS core. IS-IS running as IGP a pair of BGP route reflectors for route propagation, and a few dozens of MPLS-TE tunnels for specific tactical traffic engineering requirements. The customer’s engineering department has some questions about the use of the Overload Bit in the IS-IS networks and how it could be used to improve their current network design. Which two concepts about the Overload Bit are true? (Choose two.)
A. It can be set on a router during the startup process for a fixed period of time
B. Networks advertised within the LSPs of the respective node will become unreachable
C. It forces the midpoint MPLS-TE node to reoptimize the primary tunnels going through the OL node.
D. It can be set on a router until other interacting protocols have signaled convergence.
E. It is not recommended on BGP Route Reflectors
Answer: AD
Resources From:
1.2023 Latest Braindump2go 400-007 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/400-007.html
2.2023 Latest Braindump2go 400-007 PDF and 400-007 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1wV28HLjscHjQ8TOrCglIRRU5nn6jytDd?usp=sharing
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!